What is QKD?
Security is an endless game of cat and mouse. Throughout the history, people have built the castle walls higher and thicker, yet this has not prevented the marauders find a clever way inside. The history of cryptography narrates stories of many so-called unbreakable codes that have been cracked. This is due to the fact that conventional cryptosystems offer only computational security based on some mathematical complexity of the encryption. A breakthrough in quantum computing would leave today’s cryptosystems totally vulnerable to threats and ,for example, make electronic money instantly worthless.
Based on the firm laws of physics rather than unproven foundations of mathematical complexity, quantum cryptography provides a radically different solution for encryption and promises unconditional security. An end-to-end quantum cryptosystem includes an initial phase of quantum key distribution (QKD) and subsequent encryption. The first QKD protocol proposed by Bennett and Brassard is today widely known as BB84 which uses polarised photons to transfer the key between two points.
How does QKD work?
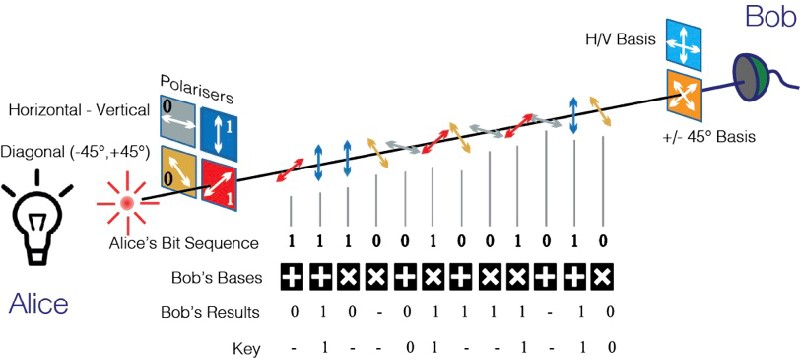
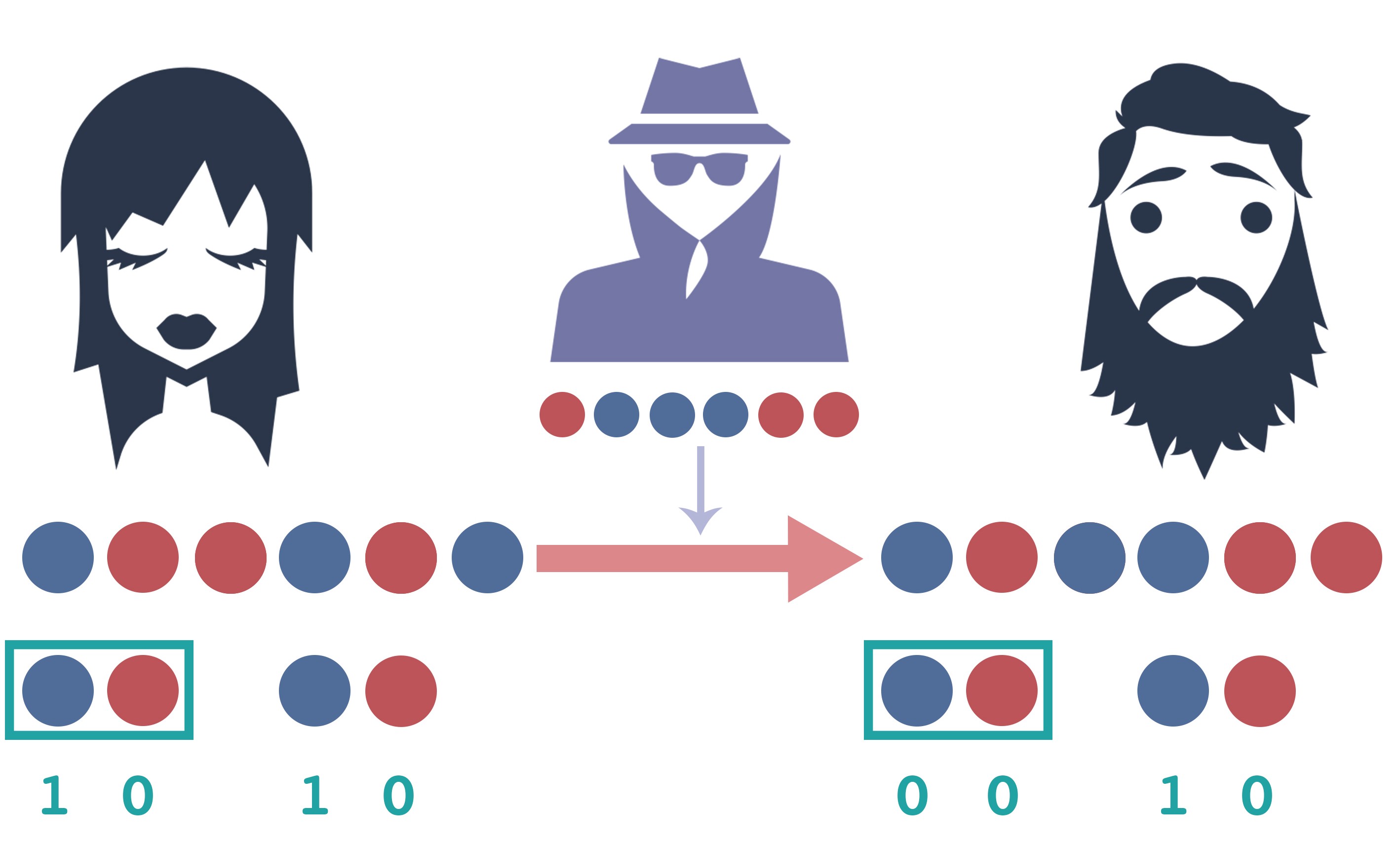
Assume the transmission of binary ones and zeroes and let them be represented by either rectilinearly (i.e., vertical or horizontal) or diagonally (i.e., left-diagonal or right diagonal) polarised photons. Alice (transmitter) randomly swaps between the rectilinear and diagonal schemes, known as “bases” in quantum cryptography terminology, during transmission. Bob (receiver) measures the photons in one of the two bases chosen at random. The choices of basis made by Alice and Bob thus comprise two independent random sequences. Therefore, about half of the basis choices will be the same and are called the “compatible” bases, and the other half will be different and are called the “incompatible” bases. After transmission and measurement, Alice and Bob compare publicly, making use for this purpose of a classical communications channel, the two independent random sets of polarization bases that were used, without revealing the polarization states that they observed. The bit values of those polarization states measured in the compatible bases yield the “sifted key.” Any adversary Eve can intercept both the quantum and the public classical channel, but thanks to the non-cloning theorem of quantum physics, she will not be able to measure the polarizations without revealing her presence, since she cannot know the random basis choices in advance.
Applications of QKD
Banking & Finance
Defence & Military Applications
Telecommunication